Integrations Guide
Splunk Integration
DMARC Defender can be integrated with Splunk to allow you to send your DMARC data to your Splunk instance for further analysis and correlation with other data sources.
DMARC Defender sends your DMARC data to Splunk in real-time as it is processed. The reports are validated, converted to JSON, enriched, split into individual records, and then sent to Splunk.
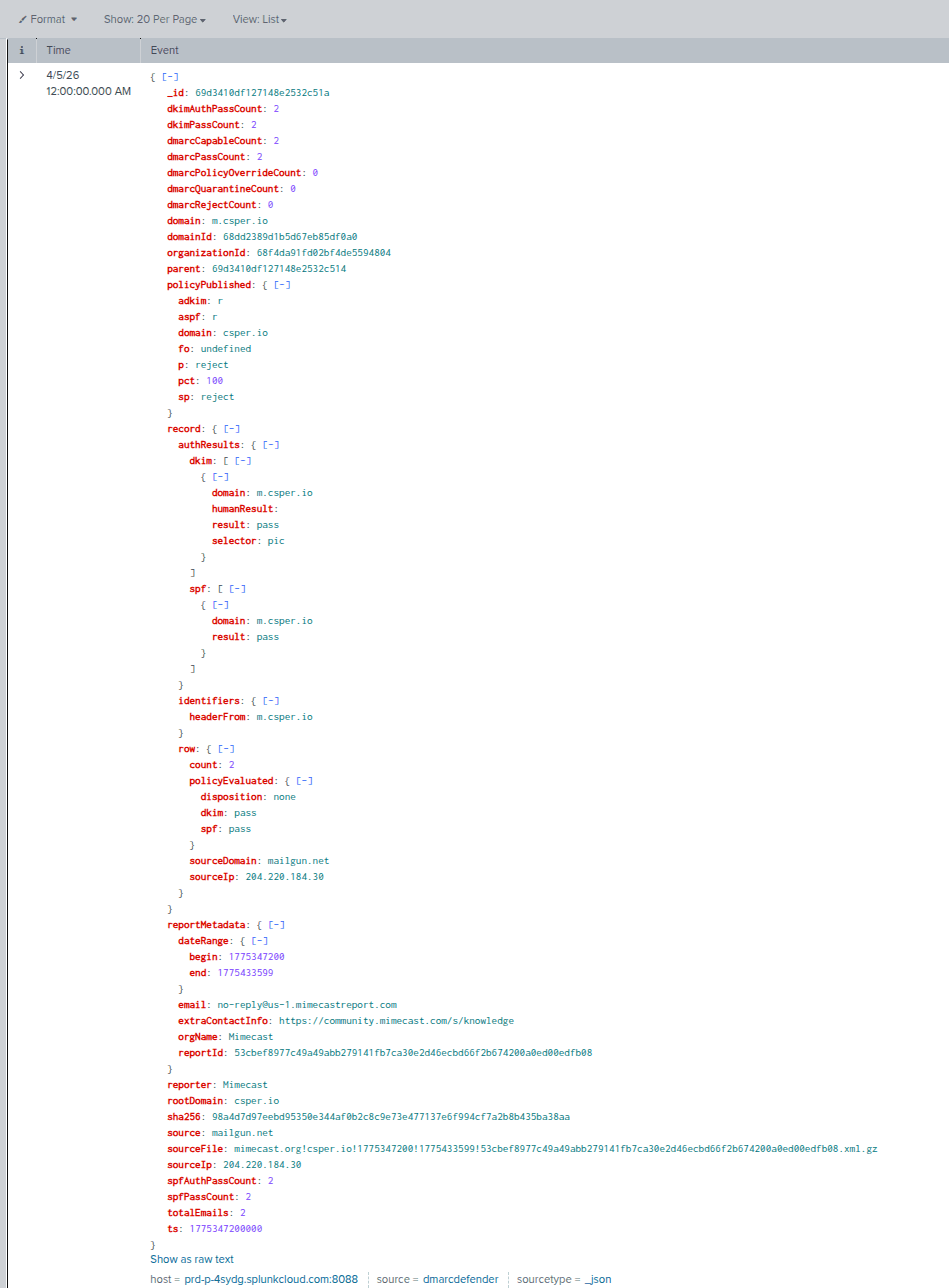
Splunk Report Example for DMARC Defender
To get started, go to your organization settings and scroll down to "Integrations". Click on "Configure" next to the Splunk integration option. You will need to provide the following information:
| Field | Description | Example |
|---|---|---|
| HEC URL | The URL of your Splunk HTTP Event Collector (HEC) endpoint. | https://splunk-instance:8088/services/collector |
| HEC Token | The token for your Splunk HEC endpoint. You can create a new token in your Splunk instance with the appropriate permissions to receive data. | 80c0b755-c742-4d2d-bb06-fad0a8be500e |
| Index | The Splunk index where you want your DMARC data to be stored. | dmarc_records |
| Skip TLS | Whether to skip TLS verification when sending data to Splunk. This is necessary if your Splunk instance is using a self-signed certificate. | true |
Datadog Integration
DMARC Defender can forward processed DMARC aggregate report parts to Datadog Logs so you can search, alert on, and correlate DMARC activity with the rest of your observability data.
Each DMARC aggregate report is parsed, validated, enriched, and split into individual report parts before being sent to Datadog as structured log events.
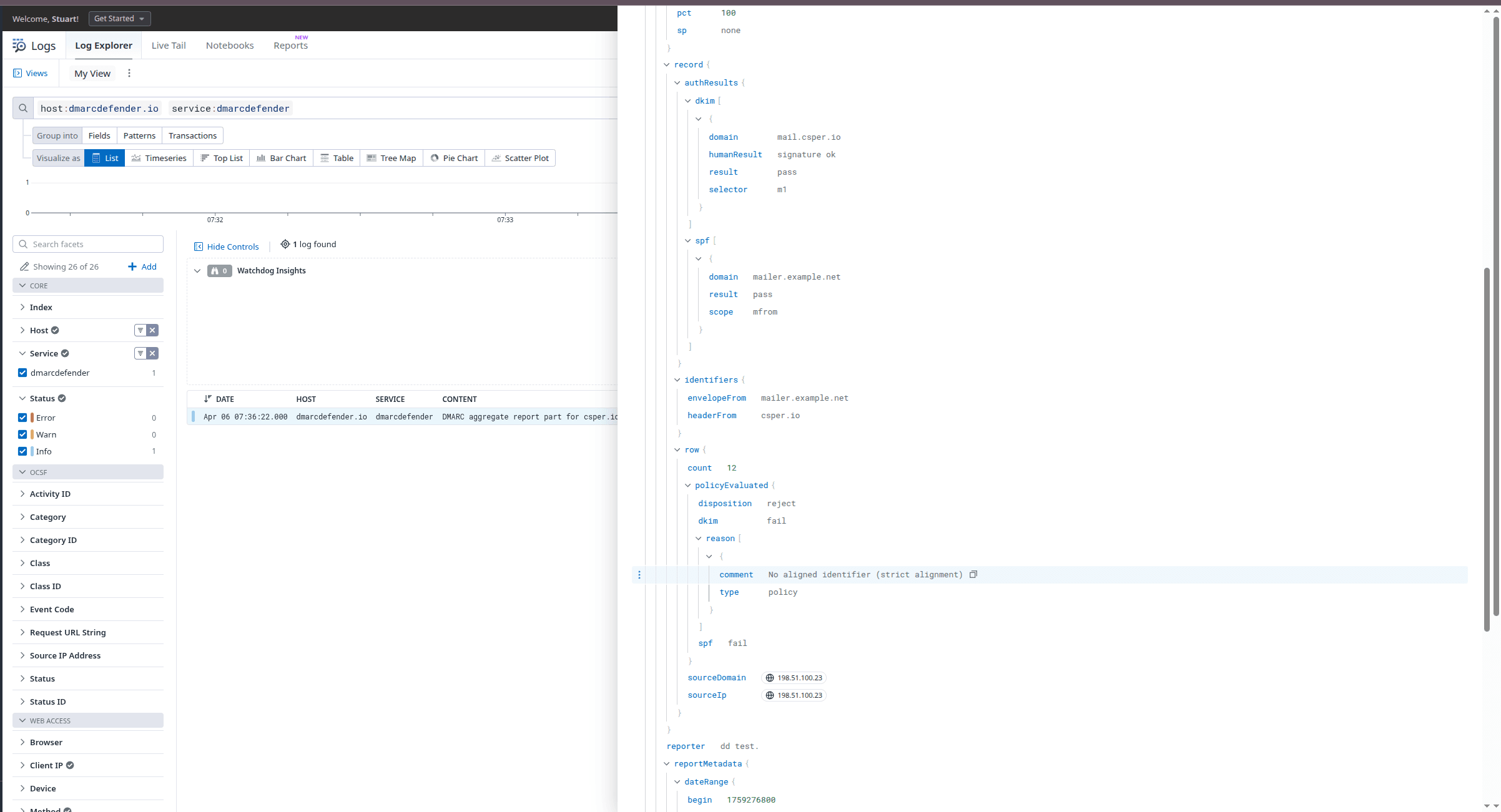
Datadog Report Example for DMARC Defender
To configure Datadog, go to your organization settings and scroll down to "Integrations". Click on "Configure" next to the Datadog integration and provide the following:
| Field | Description | Example |
|---|---|---|
| Logs Intake URL | The Datadog logs intake endpoint for your Datadog site. DMARC Defender supports US1, US3, US5, EU, AP1, AP2, and US1-FED. | https://http-intake.logs.us5.datadoghq.com/api/v2/logs |
| API Key | A Datadog API key secret used to submit logs over HTTP. This must be the 32-character API key value, not a UUID, application key, or key identifier. | b6be9d1c9c5d9945f4435b1dc2fc1bde |
DMARC Defender sends Datadog logs with the service name
dmarcdefenderand the source dmarc. Saving a Datadog integration enables forwarding immediately, and deleting the integration stops forwarding.AWS S3 Integration
DMARC Defender can forward processed DMARC aggregate report parts to an S3 bucket in your AWS account by assuming a cross-account IAM role.
Each delivery writes a batched JSON file to your bucket using the DMARC report end date as the partition path. Files are stored under a layout such as
s3://company-dmarc-logs/year=2026/month=04/day=06/report-id_x.json.To configure AWS S3, open your organization settings and choose AWS S3 in the Integrations section. Start by opening the CloudFormation quick-create link in your AWS account. Copy the generated External ID from the DMARC Defender dialog into the stack parameter, or launch the prefilled link directly from the AWS S3 settings dialog, then save the stack outputs in DMARC Defender.
Launch AWS CloudFormation Quick Create Template| Field | Description | Example |
|---|---|---|
| Bucket Name | The destination bucket where DMARC Defender will write batched JSON files. | company-dmarc-logs |
| Bucket Region | The AWS region for the destination bucket. This is used to sign PutObject requests correctly. | us-east-2 |
| Role ARN | The cross-account IAM role DMARC Defender assumes before writing objects to your bucket. | arn:aws:iam::123456789012:role/dmarcdefender-s3-integration-role |
Saving the AWS S3 integration enables forwarding immediately. Deleting the integration stops future S3 deliveries.